What is Data Protection?
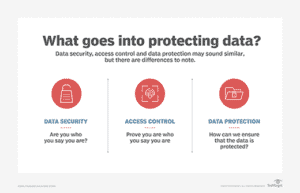
Data protection, also referred to as data privacy or information privacy, is the process of securing data and important information from being compromised or corrupted. It also involves the collection and dissemination of data and technology, the public perception and expectation of privacy, and the political and legal aspects of that data. Its goal is to find a balance between individual privacy rights while still permitting data to be used for business purposes.
With the amount of data being created and stored daily, data protection is becoming more and more imperative. As such, companies deploy strategies that allow data to be restored after any corruption or loss.
Why is Data Protection Important?
Any information that your business stores digitally needs to be properly protected. From financial information and payment details to contact information for your staff.
The importance of data protection increases as the amount of data created and stored continues to grow at unprecedented rates. There is also little tolerance for downtime that can make it impossible to access important information. Consequently, a large part of a data protection strategy is ensuring that data can be restored quickly after any corruption or loss.
What Data needs to be Protected?
Key pieces of information that are commonly stored by businesses, be that employee records, customer details, loyalty schemes, transactions, or data collection, needs to be protected. This is to prevent that data being misused by third parties for fraud, such as phishing scams, and identity theft. Protecting all this information, in accordance with the Data Protection Act, requires businesses to adhere to specific principles.
Data Protection and the Law
Data protection is not just a legal necessity, but crucial to protecting and maintaining businesses. Hence the need for a “Data Protection Act”.
What is a Data Protection Act?
A Data Protection Act controls how personal information is used by organisations, businesses or the government. A Data Protection Act contains a set of principles that organisations, government and businesses have to adhere to in order to keep someone’s data accurate, safe, secure and lawful.
House Passes Data Protection Bill (JAMAICA)
https://jis.gov.jm/house-passes-data-protection-bill/
The Data Protection Act, which will protect, in law, measures to protect the privacy and personal information of Jamaicans, was passed in the House of Representatives on Tuesday, May 19, 2020.
The Bill seeks to define the general principles for the treatment of personal data and provide for transparent oversight that will enable the public and private sectors to strengthen the protection of personal information.
The Bill further provides that data must not be transferred to a State or territory outside of Jamaica, unless that State or territory ensures an adequate level of protection for the rights and freedoms of the individual from whom the data has been collected.
https://www.loopjamaica.com/content/historic-data-protection-bill-approved-house#
The historic passage of the legislation means that Jamaica has joined the growing lists of countries whose citizens enjoy requisite safeguards of their personal information. It will now go to the Senate for debate and approval before final passage into law.
Jamaicans now have a right to know who is collecting information about them, what is being collected and what it is being used for.
The Data Protection Bill provides guidelines on how personal data should be collected, processed, stored, used and disclosed in physical or electronic form.
It requires that data should only be obtained for specific lawful purposes, with the consent of the individual, and not be further used or processed in any way incompatible with the original purpose.
∗∗∗
What is the Purpose of Data Protection?
Storage technologies that can be used to protect data include a disk or tape backup that copies designated information to a disk-based storage array or a tape cartridge device so it can be safely stored. Mirroring can be used to create an exact replica of a website or files so they’re available from more than one place. Storage snapshots can automatically generate a set of pointers to information stored on tape or disk, enabling faster data recovery, while continuous data protection (CDP) backs up all the data in an enterprise whenever a change is made.
Principles of Data Protection
The key principles of data protection are to safeguard and make available data under all circumstances, while protecting data from compromise and ensuring data privacy.
Data protection strategies are evolving along two lines: data availability and data management.
- Data availability ensures users have the data they need to conduct business even if the data is damaged or lost.
- Data Management has two key areas used in data protection: data lifecycle management and information lifecycle management.
- Data lifecycle management is the process of automating the movement of critical data to online and offline storage.
- Information lifecycle management is a comprehensive strategy for valuing, cataloging and protecting information assets from application and user errors, malware and virus attacks, machine failure or facility outages and disruptions.
Benefits of Data Protection
- Protects valuable data
- Staying ahead of the competition
- Reduced costs of development
- Protect against hackers
- Meeting current standards
- Prevents your website from going down
- Better Business Management
What are Data Protection trends?
The latest trends in data protection policy and technology include the following:
Hyper-convergence (or hyperconvergence): this is a type of infrastructure system that is largely software-defined with tightly-integrated compute, storage, networking and virtualization resources. Hyper-convergence is also called hyper-converged infrastructure.
Ransomware: this type of malware, which holds data hostage for an extortion fee, is a growing problem. Traditional backup methods have been used to protect data from ransomware. However, more sophisticated ransomware is adapting to and circumventing traditional backup processes.
Copy Data Management (CDM): this cuts down on the number of copies of data an organization must save, reducing the overhead required to store and manage data and simplifying data protection. CDM can speed up application release cycles, increase productivity and lower administrative costs through automation and centralized control. The next step with CDM is to add more intelligence.
Disaster recovery as a service: This service use is expanding as more options are offered and prices come down. It’s being used for critical business systems where an increasing amount of data is being replicated rather than just backed up.
Information Source:
https://searchdatabackup.techtarget.com/definition/data-protection
https://swiftsystems.com/guides-tips/benefits-of-data-protection/
https://www.webopedia.com/TERM/H/hyper-converged-infrastructure.html